Slashable Conditional Key Release: A Deployable Crypto-Economic Approximation of Witness Encryption
tl;dr: Witness encryption has been theoretically possible since 2013 but remains cryptographically undeployable. I’ve spent several years building a system that approximates its core properties using client-side ZK proofs, homomorphic two-party key generation, and economic slashing — with two working test implementations running today. This post is about the problem, the framing, and an honest account of where the trust boundaries sit.
The Problem
Witness encryption describes a deceptively simple primitive: encrypt a message such that it can only be decrypted by someone who can produce a valid witness for an NP statement. The condition is the key. No trusted party. No custodian. Just proof.
No secure general construction exists today. The original multilinear map construction has been broken. Evasive LWE approaches are promising but not yet deployable. Meanwhile the problems witness encryption would solve — private key recovery, identity-bound data delivery, trustless conditional access — are being patched with custodians and social recovery mechanisms that introduce exactly the failure modes cryptography is supposed to eliminate.
The Substitution
Can you build a system where a secret is cryptographically bound to a condition — where satisfying the condition is necessary and sufficient to recover the secret — without a trusted party, and without the secret ever existing in plaintext? Sealing and unsealing require communication with a processor, but the processor learns nothing about the secret or the conditions.
The answer is yes — with one substitution. Instead of the mathematical guarantee that no party can decrypt without a valid witness, you build an economic guarantee that no party will — because doing so destroys their staked capital irreversibly.
This is a crypto-economic construction, not a purely cryptographic one. The goal is not to raise the ceiling of cryptographic security but to raise the floor high enough that real UX becomes possible without sacrificing self-custody.
Proposed Primitive (informal)
A system providing:
- Confidentiality against all but a publicly slashable operator
- Cryptographic verification of release conditions
- Publicly attributable misbehavior with permissionless enforcement
- Compatible with future cryptographic substitution of the operator role
Design Principles
Before describing the construction, four principles constrain the design:
Primitive composition, not invention. Nihilium introduces no new cryptographic primitives. It composes Shamir Secret Sharing, ECElGamal homomorphic encryption, zero-knowledge proofs, EVM-based staking and slashing, and Merkle trees for timestamping — all using established libraries. The contribution is a novel configuration that achieves the target properties.
Value decomposition. What is sealed is never the asset itself — only a component worthless in isolation. A password without its encrypted file has zero standalone value. An encrypted file without its password has zero standalone value. Their combination has the full asset value. This means processor stake needs only to exceed the value an attacker could extract from the sealed component alone — which is zero under correct usage. The stake-to-asset-value comparison that initially appears problematic is the wrong frame.
Client-side proof burden. Unlike MPC and threshold systems where servers evaluate conditions, Nihilium inverts responsibility: the client proves, the processor validates. Processors remain stateless and lightweight. The condition language is infinitely extensible without processor software updates. Condition contents remain hidden from processors until unsealing.
Enforcement-only blockchain. The EVM provides immutable contracts, censorship-resistant slashing, and permissionless stake registration. In normal operation, only the datastream requires regular on-chain transactions. Clients and processors interact off-chain unless slashing or forced execution is triggered.
System Actors
The protocol has four actor types:
The Client holds secrets and bears full responsibility for cryptographic operations — defining unseal conditions, generating all zero-knowledge proofs, and executing homomorphic encryption operations within ZK circuits.
The Processor is an independent operator that commits to conditional decryption via economic stake. Processors hold an EdDSA signing key and an ECElGamal decryption key (both on Baby Jubjub). They sign sealing commitments, validate chained proof execution at unsealing time, and decrypt homomorphic ciphertexts upon successful validation. They are entirely stateless, scale horizontally without coordination, and operate independently — they are not nodes in a consensus network. Each processor is independently slashable, and processor stake is reputation capital at risk across all commitments: a single provable misbehavior forfeits the entire stake permanently.
The Datastream is a timestamping and data anchoring mechanism backed by stake. It uses a two-tier Merkle tree with a smart contract per operator updated each Ethereum block. Its critical function is anchoring the reveal value that initiates unsealing — creating mandatory public observability of all unsealing attempts. It also produces stake-backed exclusion claims: signed assertions that a value does not exist in the datastream within a specified time window. If disproven, the operator is slashed. A forced inclusion mechanism provides censorship resistance. And a full on-chain version will exist to guarantee liveness
The Blockchain (EVM) serves as the permissionless enforcement layer — processor and datastream stake registration and slashing, public key registration, and unseal condition verification contract registry.
How It Works
The project is called Nihilium. Full architecture is not yet open source, but the conceptual structure is as follows.
Two-party key generation. A processor generates one key component and the client generates a second inside a ZK circuit. The components are combined inside a homomorphic ciphertext — the final key exists only as an encrypted sum, never in plaintext during construction. The processor holds the decryption key for that ciphertext, but decrypting it without a valid proof being presented is a slashable offense. If the decrypted key is ever observed outside a valid unsealing flow, attribution is unambiguous: the processor is the only party capable of producing it. Anyone can initiate a permissionless on-chain slashing challenge; the processor must produce a valid unsealing proof or lose their stake.
Chained proofs. A composable condition pipeline supporting both ZK proof verifiers and conventional on-chain contracts. Steps pass typed signals between each other, support forking for OR-logic, and are committed to in a single hash root at sealing time — binding without revealing. Execution happens off-chain at the processor; on-chain contracts serve as the challenge layer, keeping normal operation nearly gasless. A ZK coprocessor could compact the entire chain to a constant-size proof on-chain — not yet implemented but the architecture supports it.
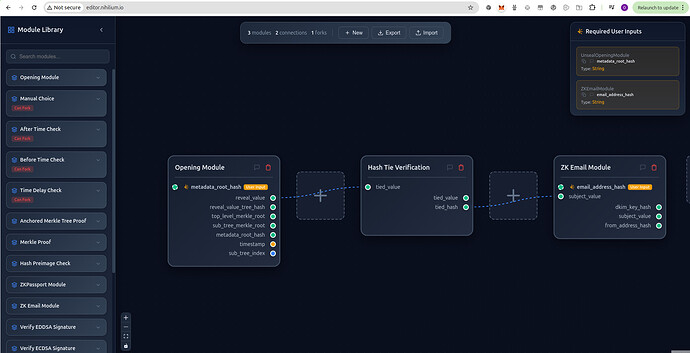
Conditions are assembled in a visual editor using a library of reusable modules (see example below).
Symmetric enforcement. The same mechanism that slashes early disclosure also enforces censorship resistance in reverse: a processor who refuses a valid unsealing request faces identical slashing. Binary ruin for either violation — not a social guarantee, the same proof operating in both directions.
Public observability. Every unsealing attempt is publicly visible before decryption occurs. To initiate unsealing, the client must insert a reveal value into the datastream — a mandatory step observable by anyone monitoring it. The owner of a sealed secret can watch for unexpected attempts in real time without trusting any party to report them. This structural observability is also what makes time-based conditions meaningful: timelocks and revocation windows only work if the unsealing attempt itself cannot be hidden. The attempt cannot be made without leaving a public, timestamped, on-chain trace — an audit property that witness encryption and MPC constructions do not provide.
Threshold redundancy. Shamir Secret Sharing across multiple independent processors gives social recovery where the guardians are contracts, not contacts. The orchestration burden — unavailable guardians, lost contact — is replaced by a threshold of economically staked actors, any subset of whom can serve the request. Recovery is a proof, not a conversation.
Where It Goes Further Than the Primitive
Timelocks. Witness encryption for timelocks still requires a real-world temporal anchor — in practice, a ZK proof of a block header from a credible, censorship-resistant chain no single party controls. Nihilium’s datastream anchors to Ethereum block height — the same chain on which slashing is enforced. This is not incidental: all temporal claims, condition verification, and economic enforcement share a single source of truth. A purely cryptographic WE timelock would require a cross-chain trust assumption to use the same anchor; here it is native.
Revocations. Witness encryption is append-only — once a condition can be satisfied, it can be satisfied. Nihilium’s datastream operators — multiple, independently staked, with at least one assumed honest and commitments publicly auditable — can produce stake-backed exclusion claims: cryptographically signed assertions that a value does not exist in the datastream between time X and Y. If it does exist and can be proven, the operator is slashed. This enables conditions of the form “valid proof AND no revocation signal in window T to T+N” — dead man’s switches with cancellation windows, fraud delay periods, regulatory intervention windows. None of these are expressible in the witness encryption primitive.
Comparison
| Property | Pure WE | Nihilium | MPC Wallets | Social Recovery |
|---|---|---|---|---|
| Deployable today | No | Yes (testnet) | Yes | Yes |
| Security model | Cryptographic | Crypto-economic | Cryptographic | Social trust |
| Publicly slashable operator | No | Yes | No | No |
| Condition expressiveness | Any NP | ZK + contracts | App-specific | None |
| Revocation | No | Yes | No | Manual |
| Censorship resistance | Inherent | Yes (symmetric) | Partial | None |
| Orchestration burden | None | None | Low–medium | High |
| Secret agnostic | Yes | Yes | No | No |
| Unsealing observability | No | Yes (datastream) | No | No |
| Compatible with future crypto substitution | N/A | Yes | No | No |
The processor is not a trusted party in the traditional sense — it is a publicly slashable operator whose misbehavior is attributable and permissionlessly challengeable.
Scope
The protocol is completely agnostic to the nature of the sealed value. Any secret representable as bytes can be sealed — private keys, passwords, medical records, legal documents, API tokens. The conditions are what matter, and conditions are defined by the application. The EVM provides the load-bearing guarantees — immutable contracts, censorship-resistant slashing, permissionless stake registration — but the applications that matter most may have nothing to do with blockchains at the user level.
Two test implementations are running: identity-verified file delivery using ZKPassport, and a “forgot password” recovery flow using ZKEmail where recovery requires replying to an email — no reset link, no 2FA, no server holding your secret. A reference implementation including the email server will be open sourced.
‘Forgot my password’: recovery.nihilium.io
Identity based file transfer: transfer.nihilium.io
Open Questions
- Can the detectability assumption — that leaked keys surface in publicly verifiable contexts — be strengthened cryptographically?
- Is there a formal security definition for slashable conditional key release as a standalone primitive, distinct from WE and MPC?
- Can the chained proof pipeline be efficiently compiled to a single ZK validity proof via coprocessor without sacrificing the composability properties?
What I Am Looking For
I am sharing this to establish the conceptual territory publicly and invite serious feedback on the framing, the trust boundary analysis, and the open questions above. Open to collaboration with researchers working on WE approximations or related primitives, and to conversations with teams building in adjacent problem spaces.
The project is Nihilium: nihilium.io , x.com/nihiliumio
— Olaf